
De la planificación al día a día del horario
Para centros de enseñanza de todo nivel y complejidad
Encuentra los horarios óptimos para tus preferencias
Depura las condiciones imposibles para obtener los mejores horarios con la IA de GHC Anti Spy 4 Scanner
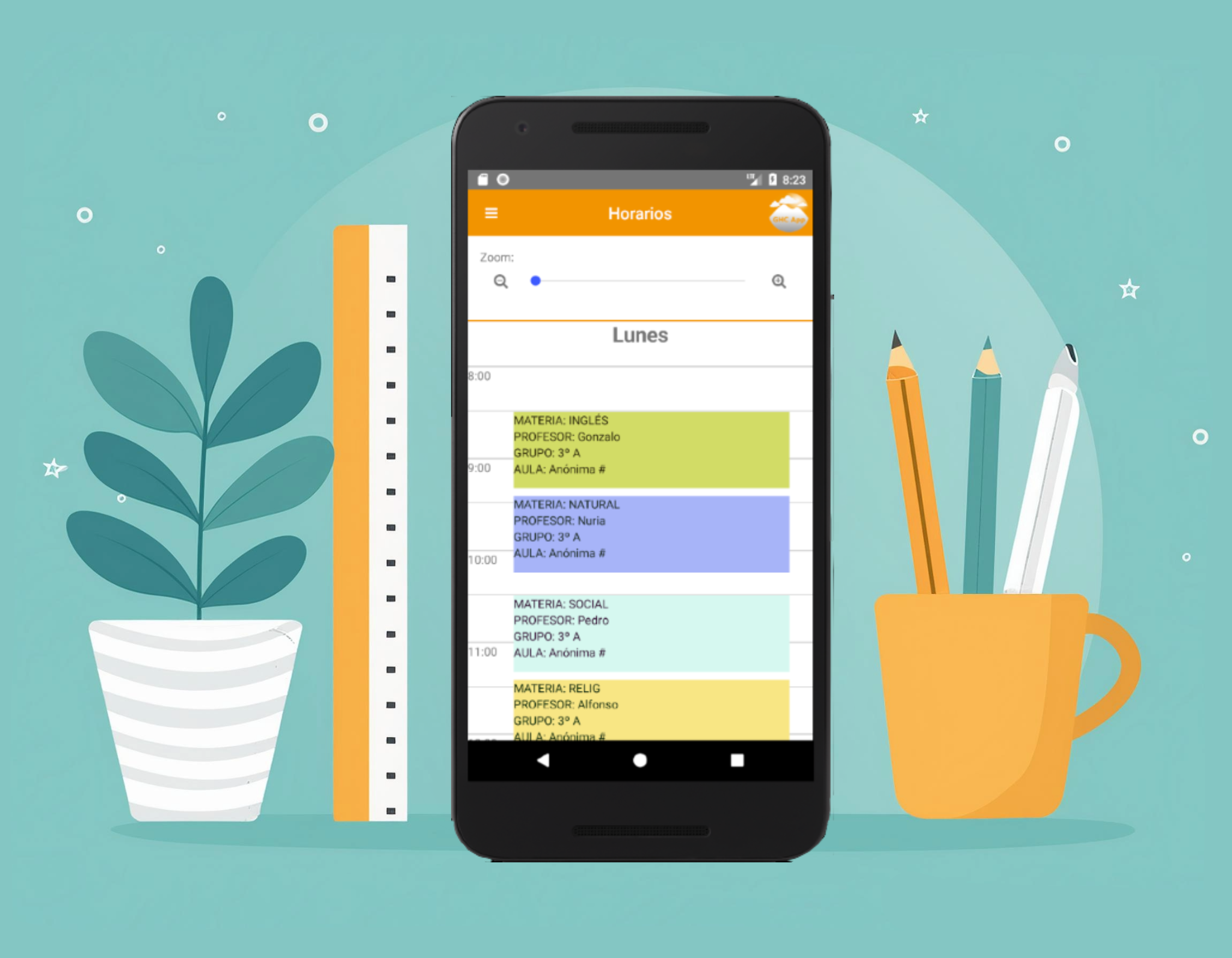
GHC App
Versiones web y móvil
Publica y visualiza horarios Scans for thousands of known surveillance signatures
Gestión sobre el calendario
Gestiona ausencias del profesorado

Te ofrecemos nuestra experiencia para ayudarte con los horarios Anti Spy 4 Scanner

 Peñalara
Peñalara